Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's Red Team Tools
Por um escritor misterioso
Last updated 31 dezembro 2024

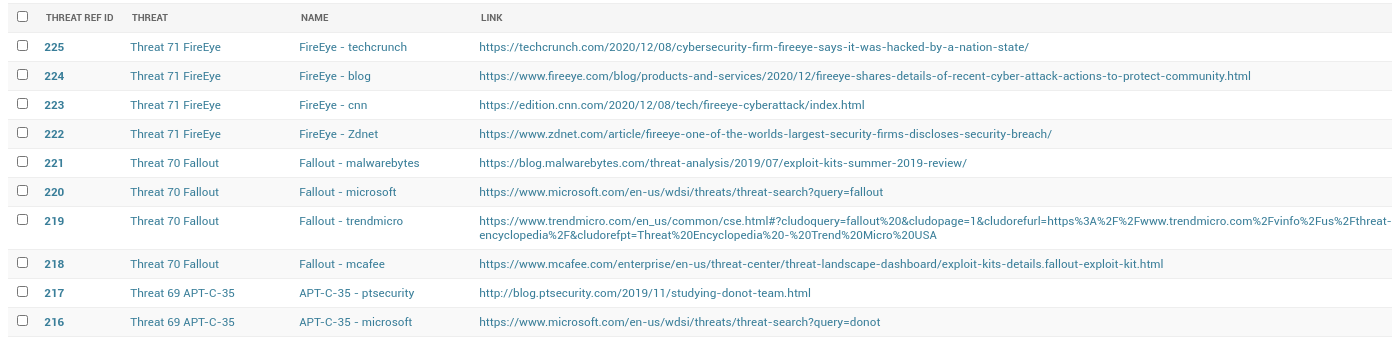
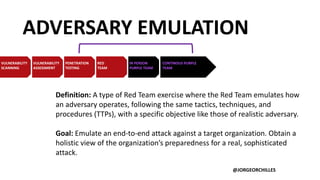
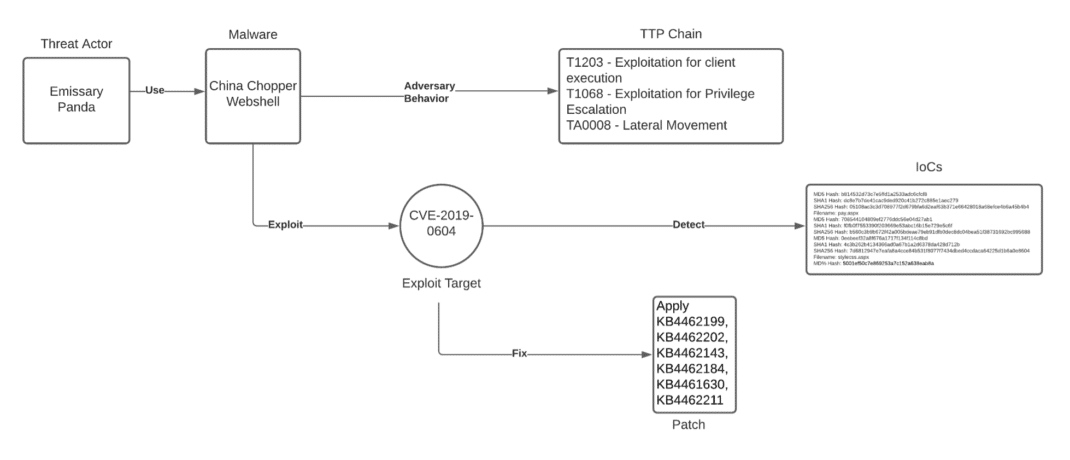
We analyzed tactics, techniques, and procedures utilized by threat actors of the FireEye’s stolen Red Team Tools. Attackers heavily used various defense evasion techniques.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
FireEye Portfolio

Red Team Assessment, Dubai
Stamus ND/NDR is Armed to Detect Stolen FireEye Red Team Tools

Red Team tactics – breaching the lines of defense – Comsec Global
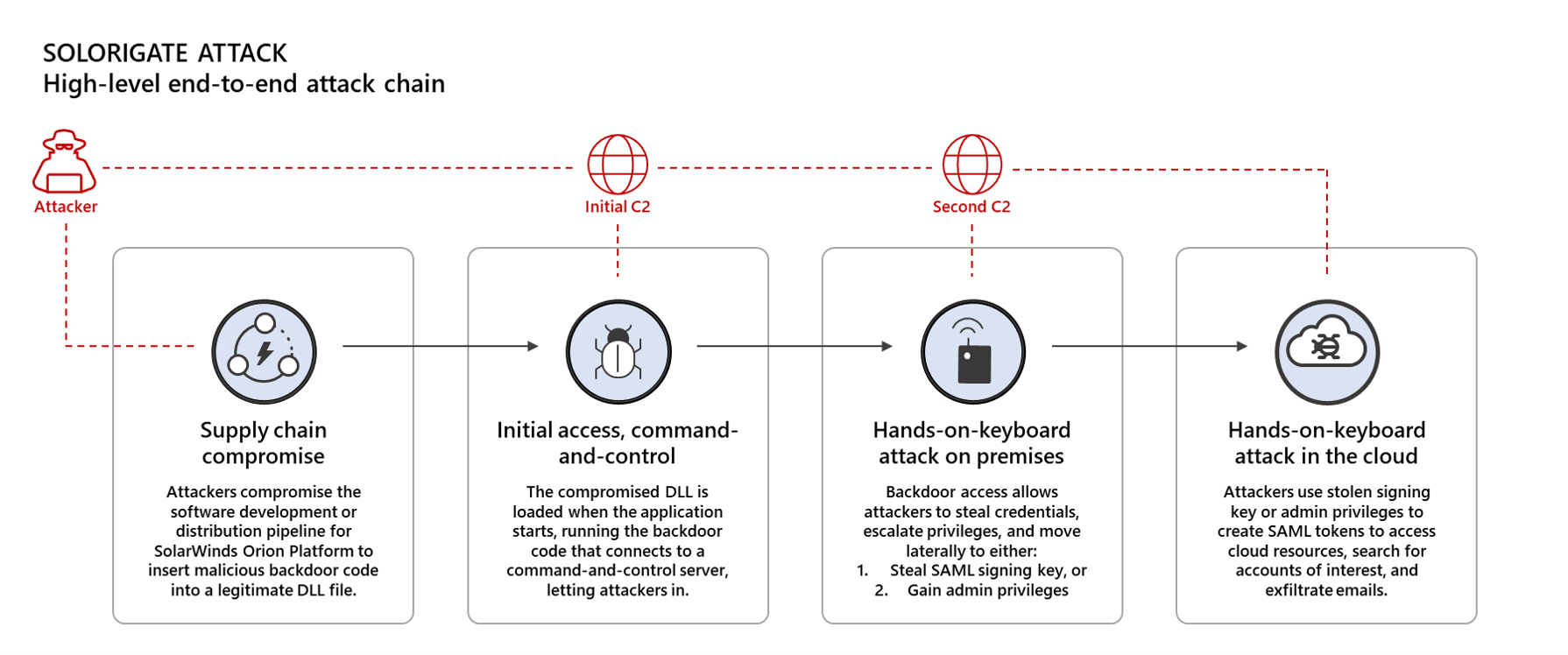
Using Microsoft 365 Defender to protect against Solorigate
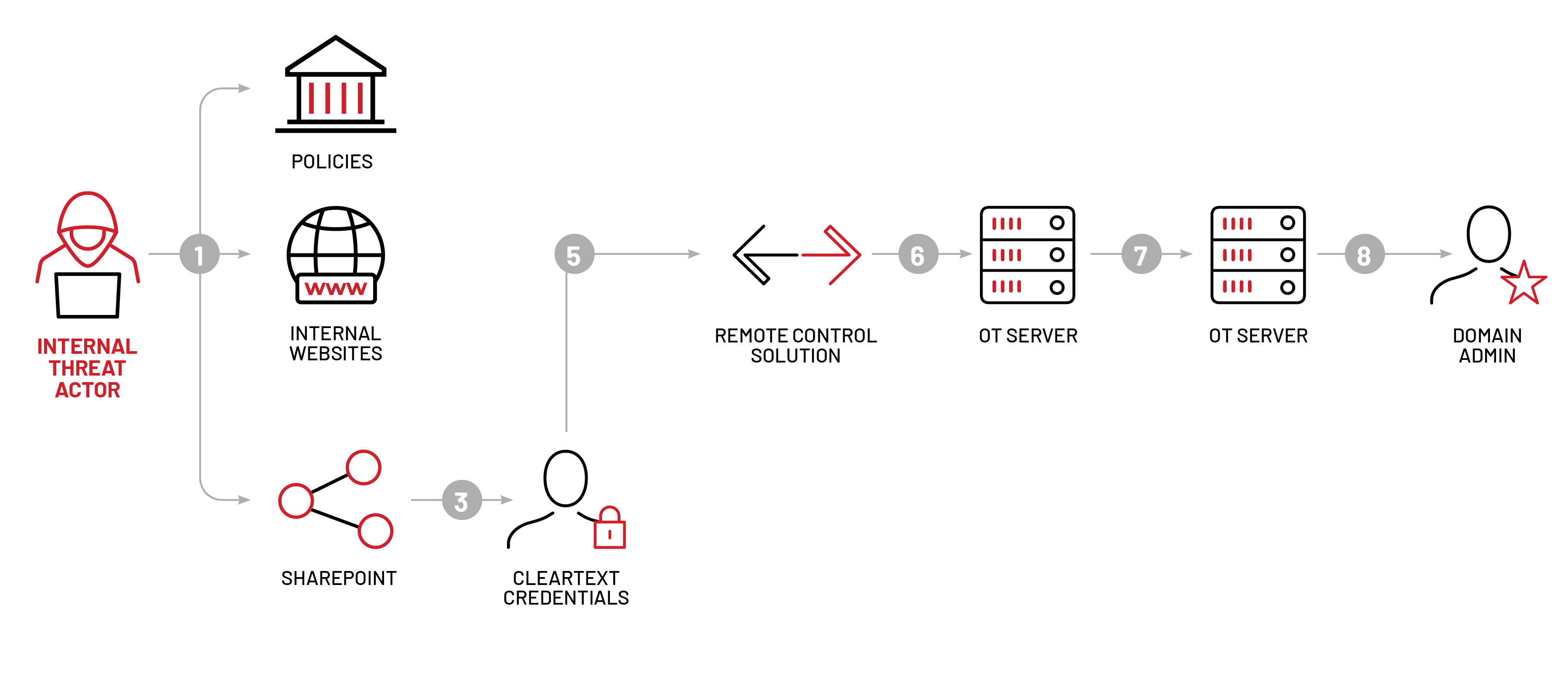
Mandiant Red Team Emulates FIN11 Tactics To Control Operational
Adversary Emulation and Red Team Exercises - EDUCAUSE

GitHub - A-poc/RedTeam-Tools: Tools and Techniques for Red Team
Unpacking the CVEs in the FireEye Breach - Start Here First

Long Term Analysis Illustrates How Risk Posed by a Vulnerability

BOLO - Be On The Lookout: FireEye Red Team Tools Stolen in Nation
Recomendado para você
-
Location Guard31 dezembro 2024
-
hwid-spoofer · GitHub Topics · GitHub31 dezembro 2024
-
 Location Spoofing, Detect Fake GPS Location31 dezembro 2024
Location Spoofing, Detect Fake GPS Location31 dezembro 2024 -
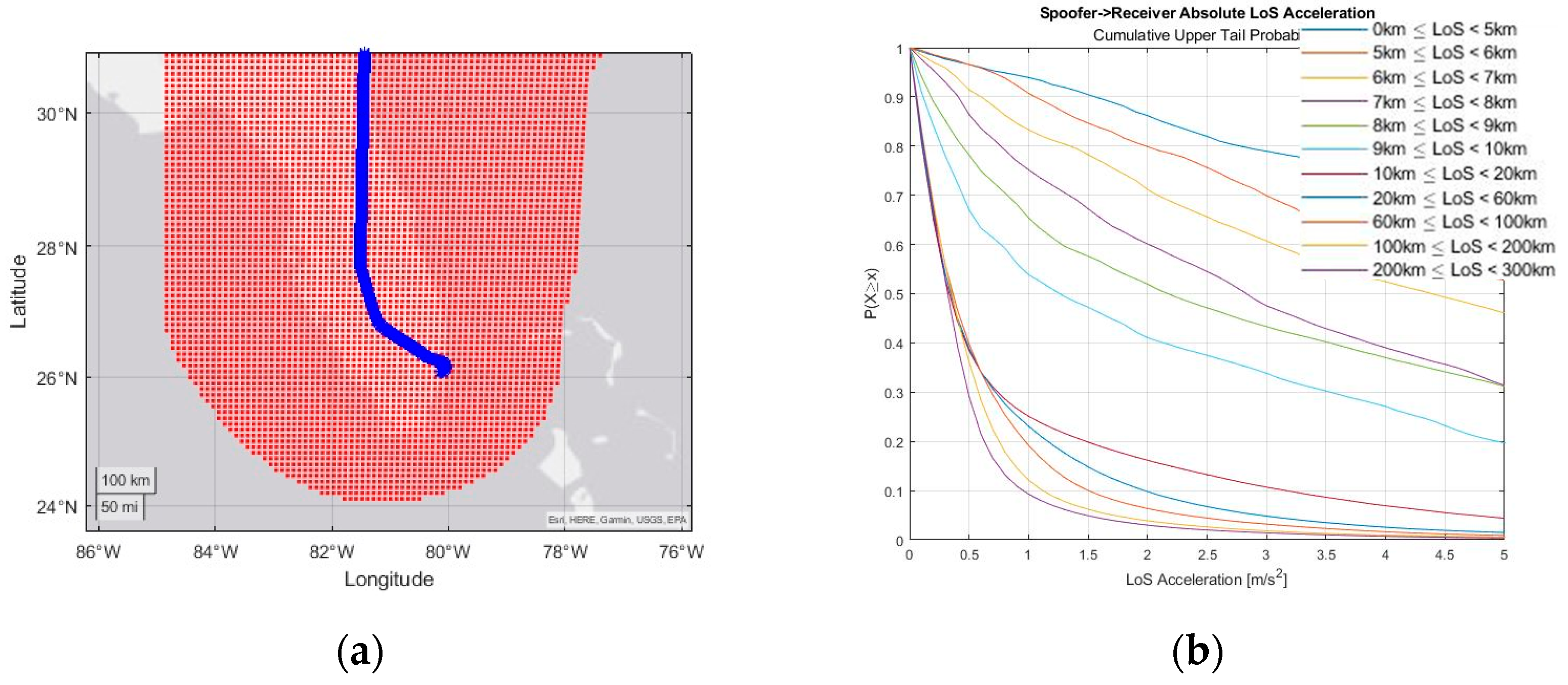 Engineering Proceedings, Free Full-Text31 dezembro 2024
Engineering Proceedings, Free Full-Text31 dezembro 2024 -
RoDAR the Equaliser31 dezembro 2024
-
Cracked Hwid Spoofer31 dezembro 2024
-
![Release] Warzone Spoofer](https://imgur.com/ByHppzY.jpg) Release] Warzone Spoofer31 dezembro 2024
Release] Warzone Spoofer31 dezembro 2024 -
 How Do MAC Spoofing Attacks Work?31 dezembro 2024
How Do MAC Spoofing Attacks Work?31 dezembro 2024 -
 GitHub - p2geedn7/redEngine: RedENGINE is the Best LUA Executor31 dezembro 2024
GitHub - p2geedn7/redEngine: RedENGINE is the Best LUA Executor31 dezembro 2024 -
 Protecting GPS From Spoofers Is Critical to the Future of Navigation - IEEE Spectrum31 dezembro 2024
Protecting GPS From Spoofers Is Critical to the Future of Navigation - IEEE Spectrum31 dezembro 2024
você pode gostar
-
 Topgolf Las Vegas - Las Vegas - Tickets31 dezembro 2024
Topgolf Las Vegas - Las Vegas - Tickets31 dezembro 2024 -
 Games of September 201531 dezembro 2024
Games of September 201531 dezembro 2024 -
 Pokémon Rojo Fuego #09 - Erika, la lider de gimnasio de tipo planta 🍀31 dezembro 2024
Pokémon Rojo Fuego #09 - Erika, la lider de gimnasio de tipo planta 🍀31 dezembro 2024 -
 Curitiba: Brazil's sustainable green gem, EPS31 dezembro 2024
Curitiba: Brazil's sustainable green gem, EPS31 dezembro 2024 -
 adidas Superstar Mens Lifestyle Shoe Black White EG4959 – Shoe Palace31 dezembro 2024
adidas Superstar Mens Lifestyle Shoe Black White EG4959 – Shoe Palace31 dezembro 2024 -
 Russian Flag, Russia, texture walls, the Russian Federation31 dezembro 2024
Russian Flag, Russia, texture walls, the Russian Federation31 dezembro 2024 -
 Handshake Gesture Emoji 3D Model $19 - .3ds .blend .c4d .fbx .max31 dezembro 2024
Handshake Gesture Emoji 3D Model $19 - .3ds .blend .c4d .fbx .max31 dezembro 2024 -
 Meeple for board games31 dezembro 2024
Meeple for board games31 dezembro 2024 -
 Roblox Camisa Branca - Caniks BR - Camisa Infantil - Magazine Luiza31 dezembro 2024
Roblox Camisa Branca - Caniks BR - Camisa Infantil - Magazine Luiza31 dezembro 2024 -
 Pokémon Yellow (Detonado - Parte 15) - Secret Key e Ginásio do Blaine!31 dezembro 2024
Pokémon Yellow (Detonado - Parte 15) - Secret Key e Ginásio do Blaine!31 dezembro 2024
