How hackers use idle scans in port scan attacks
Por um escritor misterioso
Last updated 22 dezembro 2024
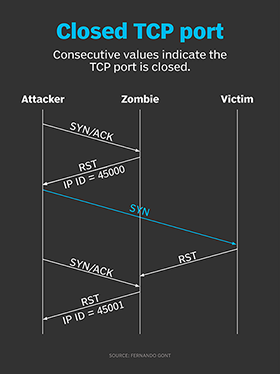
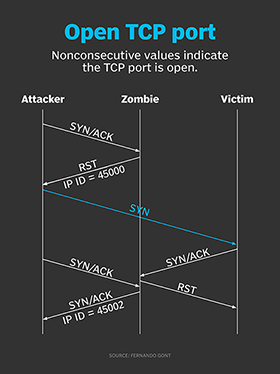
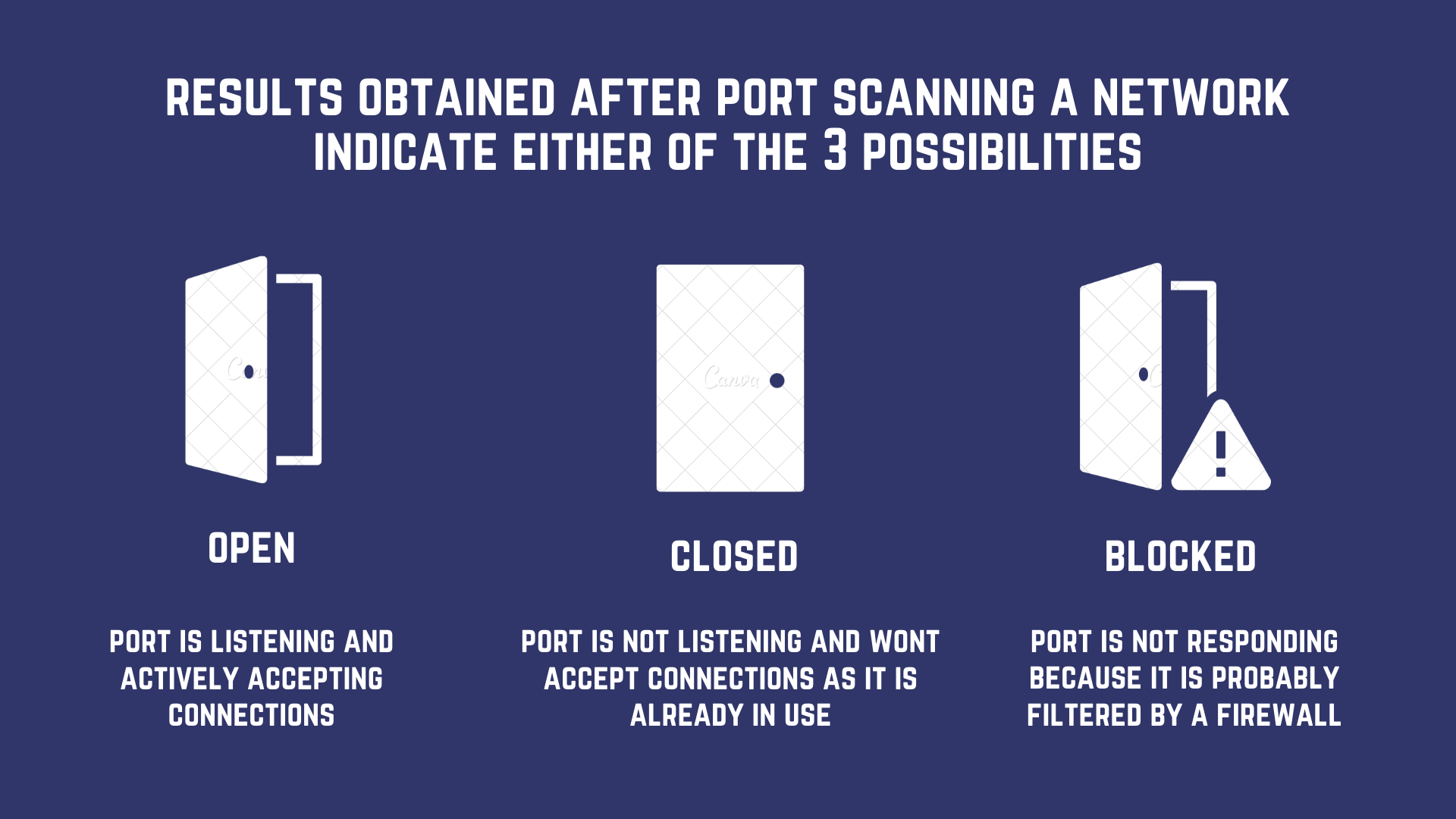
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
How hackers use idle scans in port scan attacks

Hacking techniques
What is Idle Scan? ICterra Information and Communication Technologies

Port Scanning - an overview

Port Scanning: A Comprehensive Guide for Safeguarding Cyberspace
Port Scanning based Attacks
PDF) Port Scanning: Techniques, Tools and Detection
What is a Cyber Attack? Definition and Related FAQs

NMap 101: Fun With Firewalls! HakTip 102
Recomendado para você
-
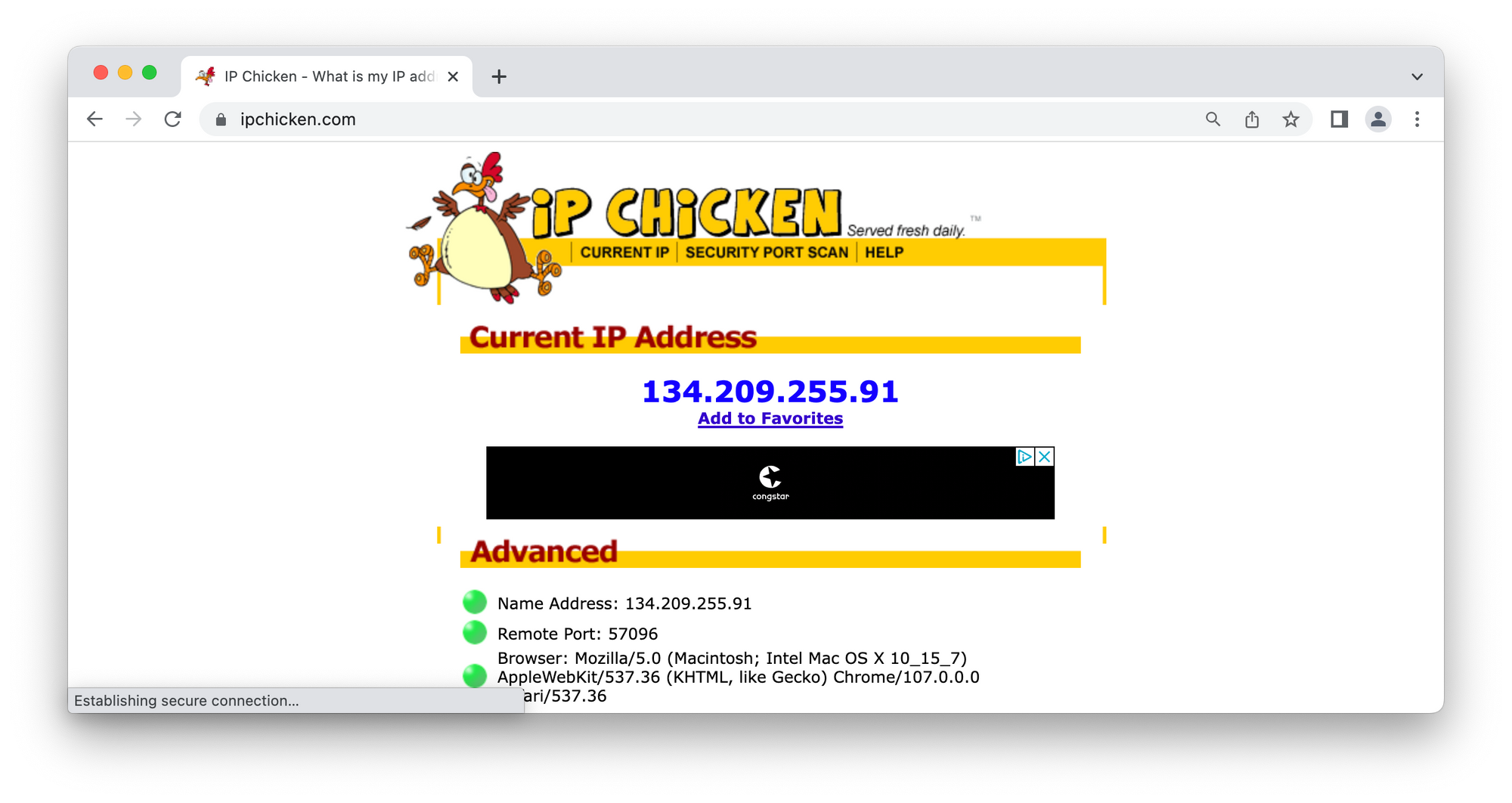
 Read own IP address and check anonymization22 dezembro 2024
Read own IP address and check anonymization22 dezembro 2024 -
 Setup OrthoInTouch with topsOrtho - OrthoInTouch - Appointment Reminders22 dezembro 2024
Setup OrthoInTouch with topsOrtho - OrthoInTouch - Appointment Reminders22 dezembro 2024 -
 IP Chicken - Served Fresh Daily22 dezembro 2024
IP Chicken - Served Fresh Daily22 dezembro 2024 -
USGPRO4: 'The gateway is unable to connect to the Internet' - but it is22 dezembro 2024
-
 Anonymous Security Scanning and Browsing22 dezembro 2024
Anonymous Security Scanning and Browsing22 dezembro 2024 -
174.218.138.250 is a publicly routable IP address is it not?22 dezembro 2024
-
![Zscaler- Source IP Anchoring [SIPA]](https://i.ytimg.com/vi/ylt74TZnS2Q/hq720.jpg?sqp=-oaymwE7CK4FEIIDSFryq4qpAy0IARUAAAAAGAElAADIQj0AgKJD8AEB-AH-CIAC0AWKAgwIABABGDwgEyh_MA8=&rs=AOn4CLAOEq5hhRYj-Kw0ehVImE5Q4ZxLDQ) Zscaler- Source IP Anchoring [SIPA]22 dezembro 2024
Zscaler- Source IP Anchoring [SIPA]22 dezembro 2024 -
 Troubleshooting NAT on Fortigate Firewall – InfoSec Monkey22 dezembro 2024
Troubleshooting NAT on Fortigate Firewall – InfoSec Monkey22 dezembro 2024 -
 Configuring private V2Ray server for bypassing internet censorship (TLS configuration)22 dezembro 2024
Configuring private V2Ray server for bypassing internet censorship (TLS configuration)22 dezembro 2024 -
 LIVE from Radiance Apr. 21, 2023 - The Panama Canal - Canal au Niveau de la Mer - Page 14 - Royal Caribbean International - Cruise Critic Community22 dezembro 2024
LIVE from Radiance Apr. 21, 2023 - The Panama Canal - Canal au Niveau de la Mer - Page 14 - Royal Caribbean International - Cruise Critic Community22 dezembro 2024
você pode gostar
-
 kujo jotaro and star platinum (jojo no kimyou na bouken) drawn by nitako22 dezembro 2024
kujo jotaro and star platinum (jojo no kimyou na bouken) drawn by nitako22 dezembro 2024 -
 Shingeki no Kyojin Attack on Titan Opening OP Guren no Yumiya22 dezembro 2024
Shingeki no Kyojin Attack on Titan Opening OP Guren no Yumiya22 dezembro 2024 -
/i.s3.glbimg.com/v1/AUTH_59edd422c0c84a879bd37670ae4f538a/internal_photos/bs/2018/5/m/agVBAbQqS5AbaBDBdTxg/24131483-1381328481989907-2442476007758809635-n.jpg) Tenor argentino Maxi Burgaro é atração em Nova Friburgo, RJ, neste sábado, Região Serrana22 dezembro 2024
Tenor argentino Maxi Burgaro é atração em Nova Friburgo, RJ, neste sábado, Região Serrana22 dezembro 2024 -
 Spider-Man 3 PS3 Pronta Entrega22 dezembro 2024
Spider-Man 3 PS3 Pronta Entrega22 dezembro 2024 -
 Kny oc base Base de desenho, Tutoriais de desenho de olhos, Tutoriais de desenho22 dezembro 2024
Kny oc base Base de desenho, Tutoriais de desenho de olhos, Tutoriais de desenho22 dezembro 2024 -
 Jogo Horizon Forbidden West Standard Edition Playstation 5 Midia Fisica - Azul - Loja Oi Place22 dezembro 2024
Jogo Horizon Forbidden West Standard Edition Playstation 5 Midia Fisica - Azul - Loja Oi Place22 dezembro 2024 -
 Quebra-cabeça Paisagens atividade cognitiva para idosos22 dezembro 2024
Quebra-cabeça Paisagens atividade cognitiva para idosos22 dezembro 2024 -
 File:Kimikiss OVA2.jpg - Anime Bath Scene Wiki22 dezembro 2024
File:Kimikiss OVA2.jpg - Anime Bath Scene Wiki22 dezembro 2024 -
 CRA-GO Conselho Regional de Administração22 dezembro 2024
CRA-GO Conselho Regional de Administração22 dezembro 2024 -
 Live-action de Yu Yu Hakusho ganha trailer e data de estreia na22 dezembro 2024
Live-action de Yu Yu Hakusho ganha trailer e data de estreia na22 dezembro 2024